SOAR Product powered by Design Thinking
Overview
Information is the most important asset for any organization, and the clients across the industry are spending handsome amounts in protecting that. Clients form blue and red teams, which go head-on to ensure the organization's IT infrastructure is cyber resilient.Blue team is a team of security professionals within a Security Operations Center(SOC) whose task is to protect the organization's information and critical assets against any kind of threat.
Red team is a team of security professional who tries to break into the systems by overcoming security controls.
Understanding Client - SOC
SOC consists primarily of a team of security analyst who works together in a 24*7 work environment to detect, analyze, respond, report, and prevents cybersecurity incidents.
A typical SOC infrastructure has IPS/IDS, firewalls, security incident and event management (SIEM), vulnerability scanning engines, endpoint protection tools, and other breach detection tools.
Current Environment
In most of the SOC, detection is automated, prevention is automated but the response is manual.
One of the main pain points of a SOC team is alert fatigue due to a deluge of false-positive alerts.
As per Gartner, below is the split of tasks in a day of a SOC analyst:
Product Strategy
There are many SOAR vendors in the market to choose from, so it is imperative for Securonix to enter the market with a product differentiation strategy. As a product manager, I find the answer in the design thinking principle.
Design thinking principles foundation is based on solving problems with a human-centric approach.
Empathize - Understanding People
It is important to understand the real pain points of the stakeholders for which the product is developed.
For Securonix SOAR the main stakeholders are security analysts, SOC managers, and Chief Information Security Officer (CISO) of the company.
I did primary research in my contact and secondary research by reading security reports to understand the user persona.
User Persona
Point of Value Statement
Considering the research analysis and understanding the SOC environment, a typical SOC has below broader problems to solve.
- A deluge of false-positive alerts leads to alert fatigue.
- Repetitive tasks in incident triaging result in demoralization.
- Limited budget, so with the increase in the volume of incidents, organizations just can't keep adding analysts to the SOC.
- Ballooning incident time to respond.
- With a mounting number of security tools, the correct utilization of tools is not realized.
POV statement: SOC is a team that needs a tool which is easy to adopt, automate the repetitive tasks, automate respond, manage incidents, collaborate, and easy to integrate with their existing infrastructure aiding them to focus on what really matters.
Product Vision and NSM
Product Vision: A vendor agnostic, cloud-native and Open SOAR product powered by AI, ML & analytics, enabling security professionals to work on what really matters.
North Star Metric this metric will bring value to the customer and is imperative for the product's long-term success.
NSM - Percentage decrease in means time to detect and respond per client.
Ideate - Generating Ideas
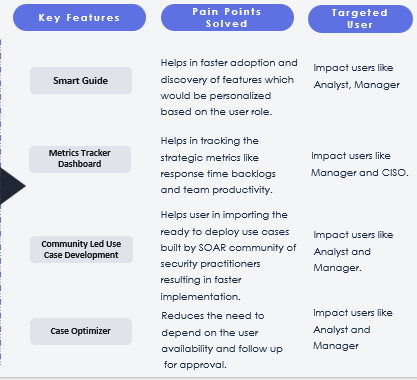
Keeping in mind the pain points of the user I could come up with the following key features which are motivated by transfer learning and brainstorming.
Product Focus & Prioritization
The product is focused on three major aspects:
- Value for Client: Automation, Optimization & Efficiency.
- Targeted Segment: B2B clients ranging from mid to large enterprises.
- Value for Organization: Revenue generation and product development.
Feature prioritization is essential for successful entry into the market and sustainable product development with limited organizational resources.
In order to prioritize the recommended features, three key parameters are considered: Reach, Impact, and Confidence.
Prototype - Creation & Implementation
Feature: Smart Guide
High Fidelity Wireframes
3. User will walkthrough to different features on that page with the visibility of how many other users with the same user profile are using which will motivate the user to explore the feature.
4. Subsequent click on the “Smart Guide” icon will aid the user in discovering relevant features.
For any feature, it is important to have the right metrics to measure its success in creating the intended value for the client.
- # of hits on the “Explore This” tab per user per week.
- % increase in the unique features being explored per user per month.
But any development comes with its own pitfalls and this feature is no different than others.
Major pitfalls which I could identify:
- In teams where all members are given the same user profile, the relevant discovery of the feature will be difficult.
Feature: Case Optimizer
- Cases that require follow-up and awaited approval from other teams can be found under "Case Optimizer".
- Approver name is visible with their status. Users can select the relevant actions to execute or schedule.
- # of times “Case optimizer” feature tab clicked per user per week.
- # of times “Take Actions” tab clicked per user per week.
Feature: Use Case Marketplace
2. User can import the pre-built use cases playbooks built by the Securonix community or by the Securonix.
3. User can see the details related to playbooks such as reviews, ratings, number of downloads, and the date on which it was published. This would help the user to make an informed decision.
4. User can click on the “See more” button for the complete description and can simulate the playbook in the simulator prior to adding it to the production.
Success Metrics:
- # of use cases playbooks imported from the Securonix marketplace.
- # of use cases published per month by the community members.
- % increase in the number of use case downloads per quarter.
Pitfalls:
- Securonix needs to verify if playbooks are safe in terms of security so that clients feel safe while transacting in the marketplace.
Feature: Metric Tracker
2. Visibility of the dashboards can be restricted based on the user profile and can be customized specifically to the organization's requirements.
3. User can export, import, edit, remove or share the dashboard with other users giving relevant permission.
4. User can create goals for the metrics in the dashboard, which notifies the user if that metric satisfies the goal conditions.
I hope you enjoyed reading this blog and, as always open to feedback. Feel free to give your valuable feedbacks in the comment section below.
Don't worry no comments would be left unheeded :)













Comments
Post a Comment